Affiliate compliance is the process of ensuring your affiliate partners follow the guidelines outlined in your affiliate marketing program terms. This process helps to prevent legal issues and protects your business’ reputation online.
An Introduction to Affiliate Compliance
Affiliate marketing programs have the potential to add great value for a company, but a few competent scammers can quickly and vastly reduce their profitability. The technical sophistication of abusive affiliates often far outweighs the merchant’s reciprocal knowledge, allowing marketing fraud to run rampant.
This guide aims to provide extensive information about fraudulent affiliate tactics so that merchants can better understand how affiliate abuse operates, the impact of it on a company, and methods for detection and prevention. We hope that this guide can serve as a step towards an overall reduction in affiliate abuse by granting merchants a deeper understanding of the ways that unethical affiliates manipulate the system.
At BrandVerity, we provide merchants and affiliate managers with tools to detect online brand and trademark abuse. Two services, PoachMark and the Affiliate Watchlist, grant clients effective management tools for their affiliate programs by detecting affiliate abuse of paid search policies and creating a continually updated list of affiliate abusers. If you have any questions or are interested in partnering with BrandVerity, please contact us.
What Is Affiliate Policy Monitoring?
Affiliate policy monitoring, or affiliate program terms monitoring, is the practice of proactive tracking and analysis of the activities affiliate partners engage in. This includes the monitoring of website content the affiliate writes, ad placements the affiliate bids on, and social media posts the affiliate makes. The goal of affiliate monitoring is to protect a brand's reputation and integrity while ensuring all affiliate partners are abiding by the rules.
Violations of Paid Search Policy
One of the most common forms of affiliate fraud arises from violations of a company’s paid search policy, often in the form of trademark bidding. In most Terms of Service agreements, companies explicitly state that affiliates cannot bid on trademarked search terms. Of course, unethical affiliates still do exactly that and they develop ever more sophisticated ways of hiding these violations from the merchant. The following section will explain and give examples of a few different ways that affiliates hide fraudulent ads from merchants as well as effective methods of countering these tactics.
Reverse IP-Geo-Targeting and Day-Parting
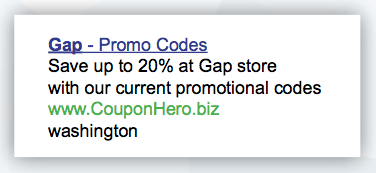
Reverse IP geo-targeting and day-parting are two of the most commonly used and fairly simple techniques affiliates use to avoid detection for paid search violations. Quite simply, affiliates set their ads to run in locations or during times of day in which they believe the merchant will not monitor them. For example, Gap’s corporate headquarters are in San Francisco. A Gap affiliate can set ads to display in every city except San Francisco, or every state except California, or only between 2am and 4am Pacific Standard Time. This means that if a Gap employee or affiliate manager searches for “Gap Coupons” from their office in California, no ads would appear and it would seem as if all affiliates were obeying the Terms of Service. If, however, a consumer searching from a computer in California at 3am, or in Nevada at any time, typed in “Gap Coupons,” a site would appear in the search results, offering a discount through an affiliate link.
There are a variety of ways to identify reverse IP geo-targeting. A commonly suggested method is to use a proxy server in order to browse with a different IP address—services such as Google Translate or Yahoo Babelfish make this process easy, albeit brittle. A number of services offer proxy servers or vpn connections that would allow you to view ads from a range of IP addresses.
It is also possible to modify your Google search query to simulate different locations and thereby trigger ads from those places. The commonly used modifiers in a Google search string are gl (country), gr (region), and gcs (city).
To simulate a location in the US, you need to use all three: Miami: &gl=us&gr=us-fl&gcs=miami New York: &gl=us&gr=us-ny&gcs=new+york
Adding these strings to the end of any already executed Google search allows you to search as if you are in those locations. If your company uses an automated monitoring system, it is important to verify that it circumvents reverse IP geo-targeting, a task usually carried out by conducting searches from multiple locations.
Warning!
- Affiliates who convert at a much higher than average ratio
- Affiliates with a substantial share of blank referrers in your network’s reporting
- Affiliates with sudden or irregular surges in orders
Disposable URLs and Front Websites
More insidious than hiding trademark bidding from merchants through IP geo-targeting or day-parting are the new methods URL hijackers have developed to minimize their discoverability. To continue running fraudulent ads even as merchants become more vigilant about trademark monitoring, abusive affiliates look for ways to make it more difficult to discover who they are. If they manage to successfully hide their affiliate ID when they purchase a paid search ad, a merchant has no way to match the ad to the affiliate who bought it.
Although the techniques to do this continue to evolve, a clear “best practice” has emerged amongst the most sophisticated hijackers. Utilizing disposable URLs and “front” websites, abusive affiliates run ads on trademarked terms while very effectively hiding their identity from merchants or affiliate managers seeking to find them.
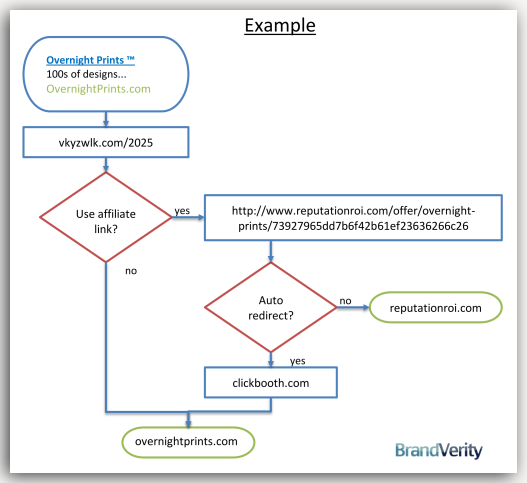
In short, the technique involves a URL hijacker purchasing ads with a destination URL that they will later discard. When a consumer visits the disposable URL, the affiliate runs a number of checks on the them and, if they pass, moves them on to a “front” website. This website effectively launders the referrer before sending the consumer through an affiliate link. This string of events can make it hard to associate the data visible at the search engine with the data visible to merchants and affiliate managers.
Disposable URLs
Because uncovering the destination URL of an ad is fairly simple, affiliates need a way to distance their fraudulent ads from their legitimate-looking affiliate properties. Disposable URLs serve this function. It’s common to see URL shorteners and raw IP addresses used as disposable URLs, but even more often, recently registered domain addresses and bulk subdomains serve this purpose.
Bulk subdomains, in particular, are incredibly inexpensive, allowing hijackers to use, change, and discard these sites quickly and frequently. For example, subdomains of the co.cc domain can be registered freely with fake registration information. This high-turnover rate makes it difficult to associate new abuse with historic abuse; by the time a merchant returns to the site to find out who the affiliate is, the link has been disabled. Further, hijackers often register these URLs under names that cannot be easily traced back to their legitimate looking affiliate properties, either by faking or making private whois information—or both.
Visitor Checks and the CSS History Hack
When the visitor arrives at the disposable domain, the affiliate runs a number of checks to decide if they should display their affiliate link. This checking process is crucial to the viability of an affiliate scam because, while not showing a link means they will not make any money, showing a link to the wrong person—a merchant, affiliate manager, or watch company like BrandVerity -- means they will be terminated from the affiliate program.
These checks range from simple procedures, such as looking at the referring URL or the visitor’s IP address, to much more complex hacks of the visitor’s browser history. One of the more complex hacks that affiliates perform on a visitor’s browser is known as the CSS History Hack. It exploits a common hole in web browsers, including Internet Explorer, Firefox, and Chrome, in order to expose information about previously visited sites. Simply, web browsers treat links you have visited differently from links you have not. By seeing what sites a visitor has previously visited, the affiliate can make a fairly accurate determination of whether or not a visitor is a merchant, affiliate manger, or network representative. Some sites that affiliate hijackers frequently search for include:
- https://www.brandverity.com/account/login/
- https://cli.linksynergy.com/cli/common/login.php
- https://nyms.linksynergy.com/owa (Hosted Exchange for Linkshare Employees)
- https://www.google.com/ads/affiliatenetwork/
- https://adcenter.microsoft.com/
If a user has visited any of these links--or fails any other check run by the affiliate-- he or she is sent immediately to the merchant website without an affiliate cookie. If they have not, they are moved on to the next phase of the process: a “front” website.
While the CSS History Hack has been closed in the most recent versions of most major browsers, unethical affiliates are constantly developing new techniques to detect visitors that they should hide their links from.
“Front” Websites
A “front” website appears to be an entirely legitimate website, often a blog, review site, or, most commonly, a coupon site. This website is the one the affiliate used apply for the affiliate program, but also serves a variety of other purposes. Its first purpose is to look like a site that could send visitors to convert. The website must act as a tangible representative of the affiliate’s supposed business model, demonstrating to a potential affiliate manager how the affiliate turns a profit and how the merchant’s brand would be promoted. This aspect is important both in terms of convincing a merchant to let the affiliate join the program in the first place, as well as in terms of seeming legitimate should a merchant or network representative visit at a later date.
Even more importantly, a second series of checks are performed on the visitor by this site, similar to the ones performed at the disposable URL, but in less depth. The purpose of this series of checks is simply to determine if the visitor should be auto-redirected or not. If all visitors were auto-redirected, the website could never seem authentic to a suspicious affiliate manager. If the user passes these checks, they will be auto-redirected to an affiliate link.
Auto-Redirects
The auto-redirect process launders the user’s referrer before sending them on to the merchant. By laundering user traffic in this way, an affiliate manages to mask the fact that the user originally arrived via a search ad. The data sent to the merchant or affiliate manager indicates only that the user came from the “front” website, and thus this traffic is interpreted as pure affiliate value add.
There are legitimate reasons to redirect users through an affiliate site, for example, an affiliate may wish to keep the search terms they are using to buy traffic private or may want to conduct their own ad tracking, meaning that it is important when tracking affiliate traffic to differentiate between proper and improper redirects. Proper redirects usually take the form of server-side 301 and 302 redirects, methods recommended by the W3C for redirection. Neither of these techniques causes “Referrer Laundering.”
Improper redirects, on the other hand, usually happen through Javascript, meta tags, and frames. Sometimes used by unsophisticated webmasters who are unable to code proper redirects, they are more commonly used by affiliates intending to launder users.
This series of processes makes it such that simply looking at the “front” website will not reveal its true source of traffic, nor the abuse conducted by the affiliate. All traffic passing from the site to the merchant will also appear legitimate.
Although disposable URLs and front websites are one common practice to launder referrers, services also exist to help affiliates hide their search terms and methods of driving traffic. Sites like referer.us and hiderefer.org launder users for the affiliate, making it very simple for them to disguise their bad practices from a merchant.
Trademark Bidding and BrandVerity
Should you choose to hire an outside company to help monitor your affiliate program, BrandVerity provides a suite of services intended to counter this kind of paid search poaching. The Affiliate Watchlist contains over 300 affiliate IDs of abusive affiliates to help screen affiliate applications and the PoachMark Pool data provides insight into other merchants’ experiences with specific affiliates. In terms of continued monitoring, PoachMark does an outstanding job of finding, attributing, and contacting affiliates who use these techniques. BrandVerity makes a consistent effort to remain on the cutting edge of affiliate poaching techniques and routinely passes this knowledge on to its clients to help them get the most out of their affiliate programs.
What Is an Affiliate Marketing Agreement?
An affiliate marketing agreement is a contract between a business (advertiser) and an affiliate (publisher) that outlines the terms and rules of the affiliate partnership. The agreement includes compensation terms like commission percentages, marketing rules about what can and cannot be done to promote the advertiser's products, a description of the advertiser's intellectual property rights and terms around how the partnership can be terminated.
What Should Be in an Affiliate Agreement?
Every affiliate agreement should include the affiliate program's commission structure, payment terms, marketing guidelines, restrictions on use of trademarks and intellectual property, termination clauses, confidentiality clauses and dispute resolution instructions.
Why Do You Need an Affiliate Agreement?
You need an affiliate agreement as a layer of legal protection for both your brand and the affiliate partners you work with. An affiliate marketing agreement offers clarity for affiliate partners by detailing commission structures, payment schedules, marketing guidelines, prohibited activities, and termination clauses. Additionally, it promotes compliance with laws and regulations like FTC disclosure and data privacy. An agreement offers intellectual property protection by specifying asset usage, and it minimizes disputes by outlining terms and providing a resolution framework.
Compliance Optimization: Transforming from a Requirement into a Growth Asset
Too often, affiliate compliance is treated as a necessary evil-a set of static checkboxes to satisfy legal minimums. However, the most successful programs view it as a powerful optimization tool. True compliance isn't about avoiding fines, it's about establishing the framework for a trusted, scalable, and high-performing affiliate marketing channel.
The Strategic Value of Proactive Compliance
Effective compliance isn't a cost center, it's an investment in your program's long-term viability and growth. When you solidify your rules and disclosures, you eliminate ambiguity. This clarity streamlines the entire affiliate lifecycle, from onboarding to commission payout. Affiliates know exactly where the lines are, allowing them to operate confidently and focus their efforts on high-value promotional tactics rather than worrying about compliance pitfalls. This not only increases affiliate retention but also improves the quality and legitimacy of the traffic they drive.
Furthermore, a well-defined compliance strategy is essential for protecting your brand equity. Every single affiliate acts as a representative of your company. In a dynamic digital marketing environment, a single non-compliant partner can erode consumer trust and attract unwanted regulatory scrutiny. Proactive monitoring and clear terms ensure that your brand's reputation remains pristine, which is perhaps the most valuable asset in any digital commerce strategy. When compliance is optimized, it becomes a seamless part of your operation, reducing risk and freeing up your team to focus on strategic marketing initiatives like expansion and recruitment.
Establishing and Enforcing the Rules
To truly optimize your program, you must set comprehensive rules and enforce them consistently. These rules must cover all critical areas: FTC disclosure requirements, permitted advertising methods (PPC, social media, email), and restricted content (trademark bidding, coupon code policy).
By leveraging compliance technology, you can automate the detection of violations and ensure swift, fair action. This systematic approach ensures that the high standards of your brand are maintained across all channels and provides an auditable history of your commitment to ethical affiliate marketing. This shift from reactive damage control to proactive brand protection is the ultimate form of optimization in the compliance landscape. It elevates your program above competitors, signaling to both consumers and high-tier affiliates that your platform is built on trust and integrity.
Continue Reading
Want to learn more? Keep reading the second part to this guide here.
